Hello Vilius,
Thanks in advance for your help.
As mentionned previously, I tried different VPN protocols between my Freebox or Synology server (both Server side) and my RUT241 (client side).
Before the wireguard protocol, I have tried OpenVPN in tunnel mode server is in the Freebox and the RUT in client mode and as I am I hope near to make it works, I prefer that you help me on that config first.
I got the config openVPN from the Server and load it into the client.
The first problem was the information that no CA certificat was found. I modified the config on the RUT side and provide the 3 certificats keys by individual files.
Now the link certification phase works, but the tunnel collapse after some seconds and the process repeat and repeat…
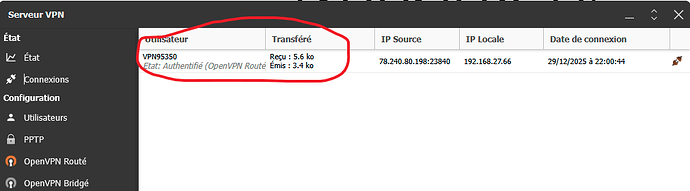
The Freebox indicate that the client is authentified and the tunnel open but for some seconds with little few traffic.
The RUT 241 use an non public address and is is able to connect to internet.
My Freebox has a public domain name and a public IPV4 address which is rechable
Here are some extract of the RUT logs:
1045 Mon Dec 29 20:54:35 2025 daemon.warn openvpn(inst1)[4096]: NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
1046 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: Control Channel MTU parms [ mss_fix:0 max_frag:0 tun_mtu:1250 tun_max_mtu:0 headroom:126 payload:1600 tailroom:126 ET:0 ]
1047 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: Data Channel MTU parms [ mss_fix:0 max_frag:0 tun_mtu:1500 tun_max_mtu:1600 headroom:136 payload:1768 tailroom:562 ET:0 ]
1048 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: TCP/UDP: Preserving recently used remote address: [AF_INET]xx.xx.xx.xx:1194
1049 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: Socket Buffers: R=[131072->131072] S=[16384->16384]
1050 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: Attempting to establish TCP connection with [AF_INET]xx.xx.xx.xx:1:1194
1051 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: TCP connection established with [AF_INET]xx.xx.xx.xx:1194
1052 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: TCPv4_CLIENT link local: (not bound)
1053 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: TCPv4_CLIENT link remote: [AF_INET]xx.xx.xx.xx:1194
1054 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: TLS: Initial packet from [AF_INET]xx.xx.xx.xx:1194, sid=eb6842a1 571be7d8
1055 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: VERIFY OK: depth=1, C=FR, O=Freebox SA, CN=Freebox OpenVPN server CA for cfdf8fb651bd46eafa37f7504c9922f2
1056 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: VERIFY KU OK
1057 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: Validating certificate extended key usage
1058 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Server Authentication
1059 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: VERIFY EKU OK
1060 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: VERIFY X509NAME OK: C=FR, O=Freebox SA, CN=Freebox OpenVPN server cfdf8fb651bd46eafa37f7504c9922f2
1061 Mon Dec 29 20:54:36 2025 daemon.notice openvpn(inst1)[4096]: VERIFY OK: depth=0, C=FR, O=Freebox SA, CN=Freebox OpenVPN server cfdf8fb651bd46eafa37f7504c9922f2
1062 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, peer certificate: 2048 bits RSA, signature: RSA-SHA256, peer temporary key: 253 bits X25519
1063 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: [Freebox OpenVPN server cfdf8fb651bd46eafa37f7504c9922f2] Peer Connection Initiated with [AF_INET]xx.xx.xx.xx:1194
1064 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: TLS: move_session: dest=TM_ACTIVE src=TM_INITIAL reinit_src=1
1065 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: TLS: tls_multi_process: initial untrusted session promoted to trusted
1067 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: PUSH: Received control message: ‘PUSH_REPLY,ping 30,ping-restart 120,dhcp-option DNS 212.27.38.253,route 192.168.27.64 255.255.255.224,route 192.168.0.0 255.255.255.0,dhcp-option DNS fd0f:ee:b0::1,ifconfig-ipv6 2a01:e0a:b84:ab18::10/124 fd0f:ee:b0::1,ifconfig 192.168.27.66 212.27.38.253,peer-id 0,cipher AES-256-CBC’
1068 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: OPTIONS IMPORT: --ifconfig/up options modified
1069 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: OPTIONS IMPORT: route options modified
1070 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: OPTIONS IMPORT: --ip-win32 and/or --dhcp-option options modified
1071 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_best_gw query: dst 0.0.0.0
1072 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_best_gw result: via 0.0.0.0 dev qmimux0
1073 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: TUN/TAP device tun_c_1 opened
1074 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: do_ifconfig, ipv4=1, ipv6=1
1075 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_iface_mtu_set: mtu 1500 for tun_c_1
1076 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_iface_up: set tun_c_1 up
1077 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_addr_ptp_v4_add: 192.168.27.66 peer 212.27.38.253 dev tun_c_1
1078 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_iface_mtu_set: mtu 1500 for tun_c_1
1079 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_iface_up: set tun_c_1 up
1080 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: net_addr_v6_add: xxxx:xxx:xxx:xxx:10/124 dev tun_c_1
1081 Mon Dec 29 20:54:37 2025 daemon.notice openvpn(inst1)[4096]: /usr/libexec/openvpn-hotplug up inst1 tun_c_1 1500 0 192.168.27.66 212.27.38.253 init
1082 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_add: xx.xx.xx.xx/32 via 0.0.0.0 dev qmimux0 table 0 metric -1
1083 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_add: 0.0.0.0/1 via 212.27.38.253 dev [NULL] table 0 metric -1
1084 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_add: 128.0.0.0/1 via 212.27.38.253 dev [NULL] table 0 metric -1
1085 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_add: 192.168.0.0/24 via 212.27.38.253 dev [NULL] table 0 metric -1
1086 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_add: 192.168.27.64/27 via 212.27.38.253 dev [NULL] table 0 metric -1
1087 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_add: 192.168.0.0/24 via 212.27.38.253 dev [NULL] table 0 metric -1
1088 Mon Dec 29 20:54:38 2025 daemon.warn openvpn(inst1)[4096]: sitnl_send: rtnl: generic error (-17): File exists
1089 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: NOTE: Linux route add command failed because route exists
1090 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Data Channel MTU parms [ mss_fix:1347 max_frag:0 tun_mtu:1500 tun_max_mtu:1600 headroom:136 payload:1768 tailroom:562 ET:0 ]
1091 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Outgoing Data Channel: Cipher ‘AES-256-CBC’ initialized with 256 bit key
1092 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Outgoing Data Channel: Using 256 bit message hash ‘SHA256’ for HMAC authentication
1093 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Incoming Data Channel: Cipher ‘AES-256-CBC’ initialized with 256 bit key
1094 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Incoming Data Channel: Using 256 bit message hash ‘SHA256’ for HMAC authentication
1095 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Initialization Sequence Completed
1096 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Data Channel: cipher ‘AES-256-CBC’, auth ‘SHA256’, peer-id: 0
1097 Mon Dec 29 20:54:38 2025 daemon.notice openvpn(inst1)[4096]: Timers: ping 30, ping-restart 120
1098 Mon Dec 29 20:54:39 2025 daemon.err openvpn(inst1)[4096]: Connection reset, restarting [0]
1099 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: TCP/UDP: Closing socket
1100 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_del: 192.168.0.0/24 via 212.27.38.253 dev [NULL] table 0 metric -1
1101 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_del: 192.168.27.64/27 via 212.27.38.253 dev [NULL] table 0 metric -1
1102 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_del: xx.xx.xx.xx/32 via 0.0.0.0 dev [NULL] table 0 metric -1
1103 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_del: 0.0.0.0/1 via 212.27.38.253 dev [NULL] table 0 metric -1
1104 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_route_v4_del: 128.0.0.0/1 via 212.27.38.253 dev [NULL] table 0 metric -1
1105 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: Closing TUN/TAP interface
1106 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_addr_ptp_v4_del: 192.168.27.66 dev tun_c_1
1107 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: net_addr_v6_del: 2a01:e0a:b84:ab18::10/124 dev tun_c_1
1108 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: /usr/libexec/openvpn-hotplug down inst1 tun_c_1 1500 0 192.168.27.66 212.27.38.253 init
1110 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: SIGUSR1[soft,connection-reset] received, process restarting
1111 Mon Dec 29 20:54:39 2025 daemon.notice openvpn(inst1)[4096]: Restart pause, 1 second(s)
It repeat the same every 11 seconds
On the Freebox interface I can see the client knoking on the door
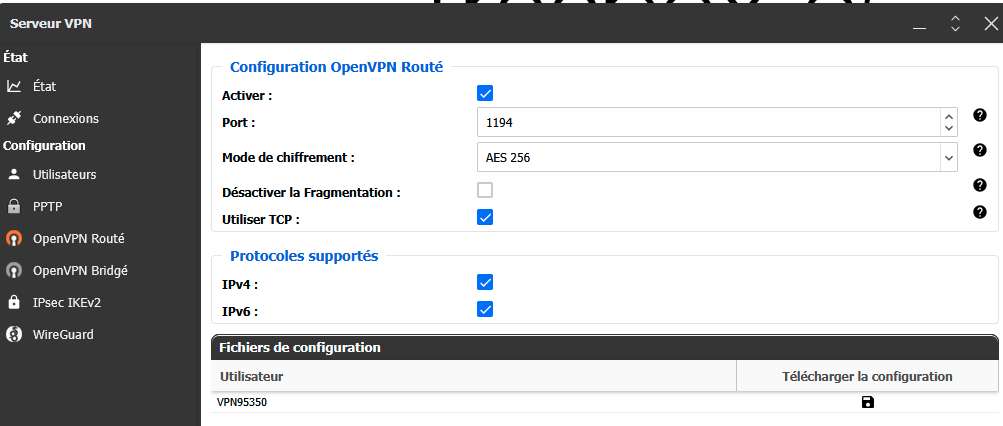
The config on the server side
Thanks
Kind regards
Michel