Introduction – What I am trying to achieve (overall design)
I’m building a small lab network with a core switch doing L3 routing and an edge router (Teltonika RUTX11) providing Internet access through a WireGuard full tunnel.
My goals are:
-
Keep inter-VLAN traffic local on the core switch (high throughput, no hair-pinning).
-
Send only Internet-bound traffic toward the Teltonika.
-
Have LAN/VLAN clients exit to the Internet exclusively via WireGuard.
-
Keep router management reachable from LAN at all times.
The switching part works as expected. The difficulty is on the Teltonika side, specifically LAN → WireGuard policy routing and firewall/NAT behavior.
Network diagram (simplified)
Internet
|
[ ISP Router ]
192.168.1.254
|
VLAN 1 / WAN subnet
192.168.1.0/24
|
+------------------+
| Teltonika RUTX11|
|------------------|
| WAN: 192.168.1.240
| LAN: 192.168.240.1
| WG : protonch |
+------------------+
|
| trunk / uplink
|
+-----------------------------+
| Core L3 Switch |
|-----------------------------|
| SVIs / Routing |
| VLAN 230 – 192.168.230.2 |
| VLAN 240 – 192.168.240.2 |
| VLAN 250 – 192.168.250.2 |
+-----------------------------+
|
Access / Wi-Fi
Clients in VLAN 240
192.168.240.0/24
Switching side
VLANs & SVIs
-
Multiple VLANs (230 / 240 / 250).
-
Each VLAN has an SVI on the core switch.
-
Inter-VLAN routing happens locally on the switch (this works perfectly).
Policy-Based Routing (PBR) on the switch
-
I initially tested PBR on VLAN 240 to force Internet traffic toward the Teltonika.
-
PBR was removed later to simplify troubleshooting.
-
At this stage, I am not relying on switch PBR anymore.
Switching is stable and not the problem.
Teltonika design intent
-
Teltonika RUTX11 is the Internet gateway.
-
Internet access should go only via WireGuard (full tunnel).
-
WAN is used only to establish the tunnel.
-
LAN clients must:
-
Access the router (SSH / GUI) normally.
-
Reach the Internet through WireGuard
-
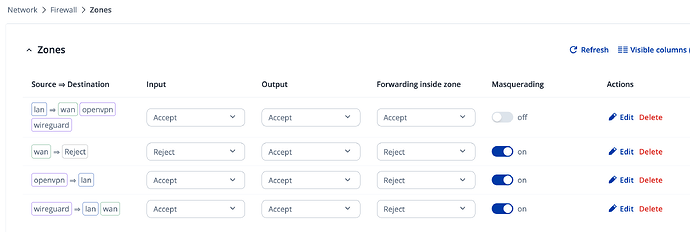
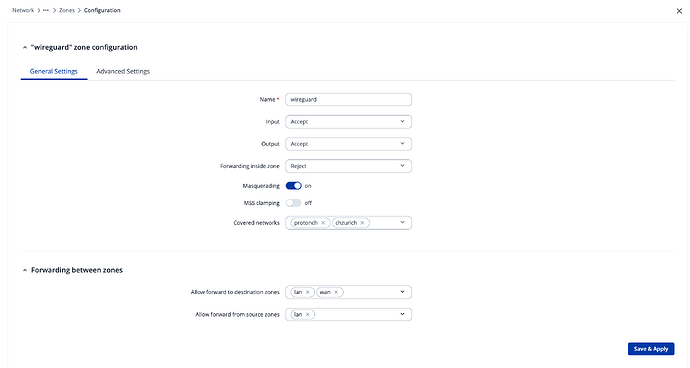
Firewall zones (summary)
Zones present:
-
lan -
wan -
wireguard(coversprotonch) -
openvpn -
another unused zone
Firewall configuration:
-
wireguardzone: ACCEPT / ACCEPT / ACCEPT, masquerading enabled -
Forwarding exists:
lan → wireguard -
NAT exists on WireGuard zone
Example verification:
uci show firewall | grep forwarding
iptables -t nat -L POSTROUTING -v -n
The problem
Symptoms
-
Router itself can access Internet via WireGuard.
-
LAN / Wi-Fi clients cannot access Internet.
-
When I tried policy routing for LAN, LAN clients lost access to the router itself (SSH/GUI), although WAN SSH still worked.
ip route add default dev protonch table 100
ip rule add from 192.168.240.0/24 lookup 100 priority 100
Result:
-
LAN traffic routed into WireGuard
-
Router replies to LAN clients also routed into WireGuard
-
SSH/GUI from LAN to
192.168.240.1stops working
I tried mitigating with:
ip rule add from 192.168.240.1 lookup main priority 50
…but LAN access remained unreliable.
What I need help with (Teltonika side)
-
Correct way to route LAN clients via WireGuard full tunnel
- Without breaking LAN access to the router itself.
-
Best practice on Teltonika for this use case:
-
Pure
ip rulebased routing? -
fwmark+ policy routing? -
Built-in Teltonika VPN policy routing feature?
-
-
Minimal and correct firewall + NAT setup for:
-
LAN → WireGuard → Internet
-
While keeping router management local.
-
Expected final behavior
-
LAN clients:
-
Gateway: Teltonika LAN IP
-
Internet exit IP = WireGuard provider
-
Can SSH / manage router normally
-
-
Router:
-
Managed from LAN and WAN
-
WAN used only to maintain tunnel
-
-
Switching:
-
Inter-VLAN stays local
-
Internet traffic exits via Teltonika only
-