Hello,
I’m using two 4G RUT951 routers.
You’ll find below configurations of both ipsec and the result of ipsec statusall just after.
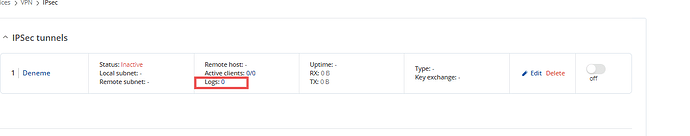
What I remarked is that when Remote endpoint (in GUI) or gateway (in CLI) is defined on the router, IPSEC won’t work for this router. But if the other router let this parameter empty for GUI or not set for CLI, IPSEC tunnel works on one way only. This is the part I don’t understand and I hope someone here will help. Sensitive data have been replaced by “X”.
Router 1 : 192.168.1.254/24 :
root@router1:~# cat /etc/config/ipsec
config ipsec
option rtinstall_enabled '1'
option make_before_break '0'
config remote 'r1_alpha'
list transport 'r1_alpha_c'
option multiple_secrets '0'
option remote_identifier '192.168.2.254'
option authentication_method 'psk'
option pre_shared_key '0x6970736563'
option local_identifier '192.168.1.254'
option force_crypto_proposal '1'
list crypto_proposal 'r1_alpha_ph1_1'
option enabled '1'
option gateway 'XXX.XXX.XXX.XXX' # <============== ?
config connection 'r1_alpha_c'
option remote_firewall '0'
option defaultroute '0'
list crypto_proposal 'r1_alpha_ph2_1'
option mode 'start'
option forceencaps '0'
option comp_mode '0'
option type 'tunnel'
option force_crypto_proposal '1'
option dpd '0'
option keyexchange 'ikev2'
option flush '0'
option local_firewall '0'
option aggressive '0'
list local_subnet '192.168.1.0/24'
list remote_subnet '192.168.2.0/24'
config proposal 'r1_alpha_ph1_1'
option encryption_algorithm 'aes256'
option hash_algorithm 'sha256'
option dh_group 'modp2048'
config proposal 'r1_alpha_ph2_1'
option encryption_algorithm 'aes256'
option hash_algorithm 'sha256'
option dh_group 'modp2048'
Router 2 : 192.168.2.254/24` :
In the above configuration, VPN works from router 2 → 1 because no remote endpoint (gateway) have been set in the router 2. If I put the public IP address or FQDN of router 1, it won’t work anymore…
root@router2:~# cat /etc/config/ipsec
config ipsec
option rtinstall_enabled '1'
option make_before_break '0'
config remote 'r1_alpha'
list transport 'r1_alpha_c'
option multiple_secrets '0'
option remote_identifier '192.168.1.254'
option authentication_method 'psk'
option pre_shared_key '0x6970736563'
option local_identifier '192.168.2.254'
list crypto_proposal 'r1_alpha_ph1_1'
option force_crypto_proposal '1'
option enabled '1'
config connection 'r1_alpha_c'
option remote_firewall '0'
option defaultroute '0'
option mode 'start'
option forceencaps '0'
option comp_mode '0'
option type 'tunnel'
option dpd '0'
option keyexchange 'ikev2'
option flush '0'
option aggressive '0'
list crypto_proposal 'r1_alpha_ph2_1'
option force_crypto_proposal '1'
option local_firewall '0'
list local_subnet '192.168.2.0/24'
list remote_subnet '192.168.1.0/24'
config proposal 'r1_alpha_ph1_1'
option encryption_algorithm 'aes256'
option hash_algorithm 'sha256'
option dh_group 'modp2048'
config proposal 'r1_alpha_ph2_1'
option encryption_algorithm 'aes256'
option hash_algorithm 'sha256'
option dh_group 'modp2048'
Now let see what’s happen on each router.
root@router1:~# ipsec statusall
Status of IKE charon daemon (strongSwan 5.9.6, Linux 5.15.149, mips):
uptime: 56 minutes, since Jul 05 15:19:49 2024
worker threads: 11 of 16 idle, 5/0/0/0 working, job queue: 0/0/0/0, scheduled: 1
loaded plugins: charon aes des sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pgp pem openssl pkcs8 xcbc hmac kernel-netlink socket-default stroke vici updown eap-identity eap-mschapv2 xauth-generic
Listening IP addresses:
192.168.1.254
fd64:a098:3b0e::1
10.84.XXX.XXX
Connections:
r1_alpha-r1_alpha_c: %any...193.YYY.YYY.YYY IKEv2
r1_alpha-r1_alpha_c: local: [192.168.1.254] uses pre-shared key authentication
r1_alpha-r1_alpha_c: remote: [192.168.2.254] uses pre-shared key authentication
r1_alpha-r1_alpha_c: child: 192.168.1.0/24 === 192.168.2.0/24 TUNNEL
Security Associations (0 up, 1 connecting):
r1_alpha-r1_alpha_c[23]: CONNECTING, 10.84.XXX.XXX[%any]...193.YYY.YYY.YYY[%any]
r1_alpha-r1_alpha_c[23]: IKEv2 SPIs: c633152a7a09babe_i* 0000000000000000_r
r1_alpha-r1_alpha_c[23]: Tasks active: IKE_VENDOR IKE_INIT IKE_NATD IKE_CERT_PRE IKE_AUTH IKE_CERT_POST IKE_CONFIG CHILD_CREATE IKE_AUTH_LIFETIME IKE_MOBIKE
root@RUT951:~# ipsec status
Security Associations (0 up, 1 connecting):
r1_alpha-r1_alpha_c[23]: CONNECTING, 10.84.XXX.XXX[%any]...193.YYY.YYY.YYY[%any]
root@router2:~# ipsec statusall
Status of IKE charon daemon (strongSwan 5.9.6, Linux 5.15.149, mips):
uptime: 39 minutes, since Jul 05 15:55:29 2024
worker threads: 11 of 16 idle, 5/0/0/0 working, job queue: 0/0/0/0, scheduled: 0
loaded plugins: charon aes des sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pgp pem openssl pkcs8 xcbc hmac kernel-netlink socket-default stroke vici updown eap-identity eap-mschapv2 xauth-generic
Listening IP addresses:
192.168.2.254
fdd4:f74e:9ac6::1
10.84.XXX.XXX
Connections:
r1_alpha-r1_alpha_c: %any...%any IKEv2
r1_alpha-r1_alpha_c: local: [192.168.2.254] uses pre-shared key authentication
r1_alpha-r1_alpha_c: remote: [192.168.1.254] uses pre-shared key authentication
r1_alpha-r1_alpha_c: child: 192.168.2.0/24 === 192.168.1.0/24 TUNNEL
Security Associations (0 up, 0 connecting):
none
Any help would be appreciate, I’m totally stuck there …