Hello,
I previous installations, I had managed to use RUT95x routers with Strongswan configured with a “roadwarrior” configuration, with the responder using an X.509 certificate and the initiator using EAP-MSCHAPv2.
Considering the RUT95x is the device on the mobile network, that’s the initiator.
I was able to get that to work with the old configuration mechanism (ipsec.conf) by passing a custom option.
In the /overlay/upper/etc/config/ipsec config file (and even eventually in the GUI):
list custom 'leftauth=eap-mschapv2'
list custom 'eap_identity=rut956_xxxxx'
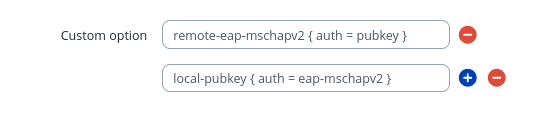
The problem is that those options are completely meaningless when using the new swanctl configuration mechanism. Those custom options do end up in the correct connection block, but they do nothing.
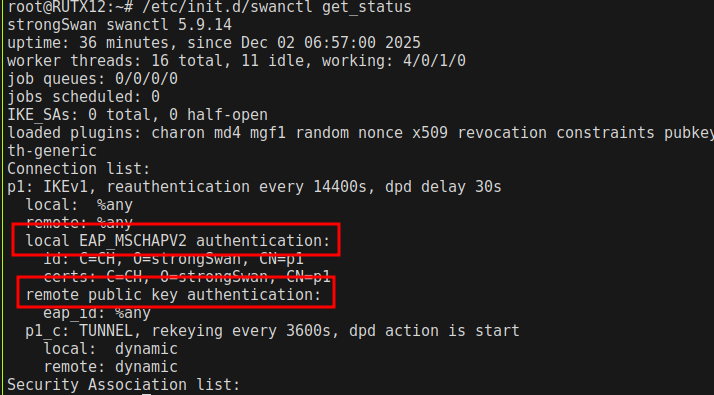
The other problem is that, when you select EAP as the authentication method in the GUI, the script that converts the options into the swanctl.conf file assumes that the router is going to be using an X.509 cert and that the remote party will be using EAP.
I need the other way around (and that’s the way that makes more sense in a mobile scenario, where the mobile router will have a dynamic IP address, often behind CGNAT too).
At the moment, with firmware 00.07.18.3, you the generated swanctl.conf looks like this:
remote-eap-mschapv2 {
auth = eap-mschapv2
eap_id = %any
id = "xxxxxx"
}
local-pubkey {
auth = pubkey
certs = /etc/uhttpd.crt
id = "yyyyyyy"
}
Digging into the scripts, it looks like this comes from /etc/init.d/swanctl, around line 840:
case $auth_method in
xauth)
config_round "local" "psk"
config_round "remote" "psk"
config_round "local" "xauth"
config_round "remote" "xauth"
;;
eap-mschapv2)
config_round "remote" "eap-mschapv2"
config_round "local" "pubkey"
;;
pkcs12)
config_round "local" "pubkey"
config_round "remote" "pubkey"
;;
*)
config_round "local" "$auth_method"
config_round "remote" "$auth_method"
;;
esac
It somehow makes the assumption that if the user picks “eap-mschapv2” in the GUI, then it’s the remote party that should be using “eap-mschapv2” and local should be using “pubkey”.
Could Teltonika please fix this?
It might even be worth showing auth options for both local and remote parties in the GUI (instead of making the assumption).
More generally, it seems that the migration from ipsec.conf to swanctl has broken other configurations.
Could you please fix the option conversion scripts so that we can actually have useful custom options, in particular options that can affect the configuration within sub-blocks in the swanctl.conf file? Failing that, could we have the option to revert to the ipsec.conf configuration style, maybe as an advanced option?
Thank you.