Hi,
it’s me again ![]() Last time for today, I promise.
Last time for today, I promise.
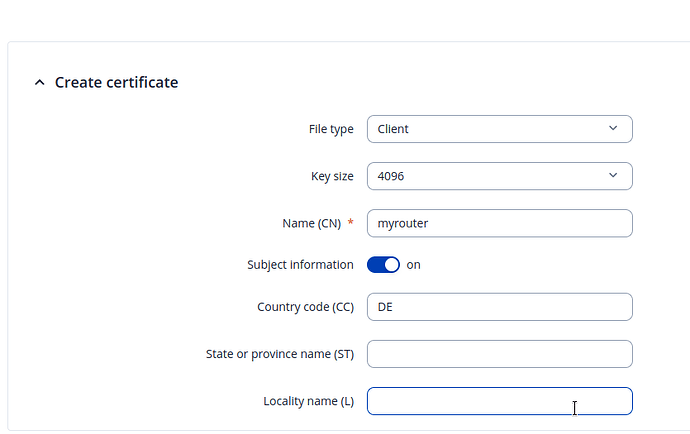
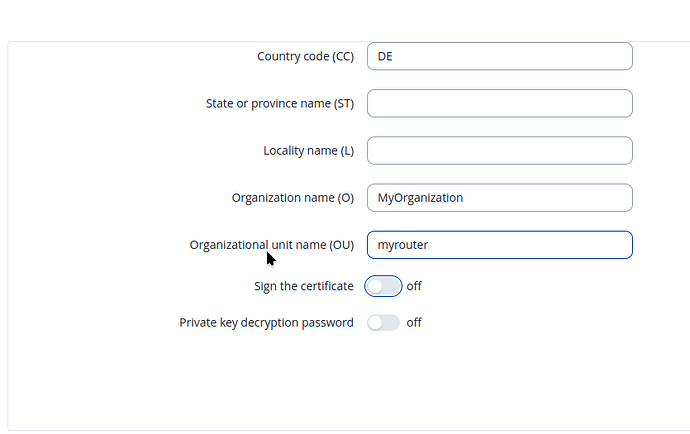
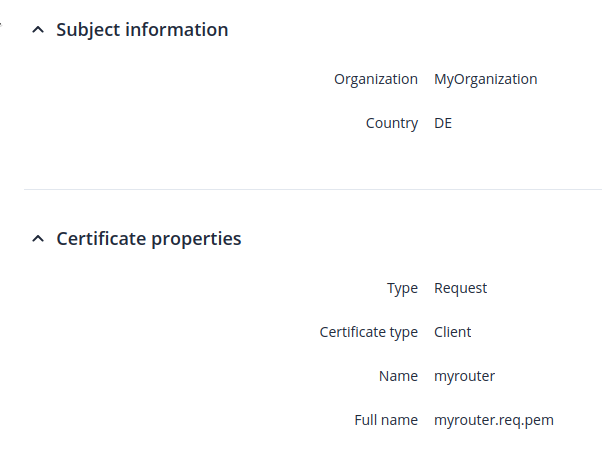
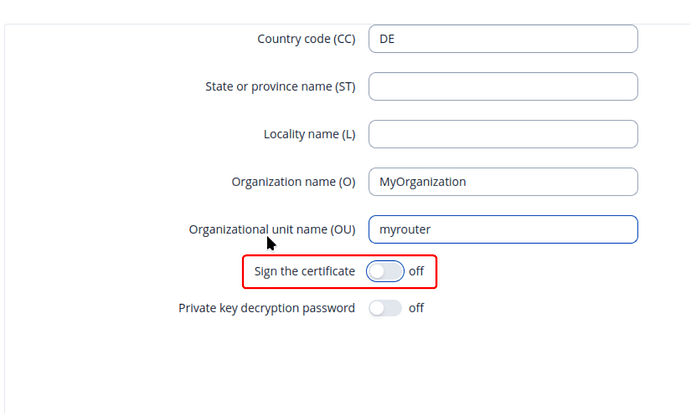
Since I need to make some progress, I now use the RMS to access my remote device’s WebUI, doing things manually. I used System => Administration => Certificate to generate a certificate request for a client certificate and a corresponding private key:
Note that “Private key decryption password” is “Off”. We’ll need that information later.
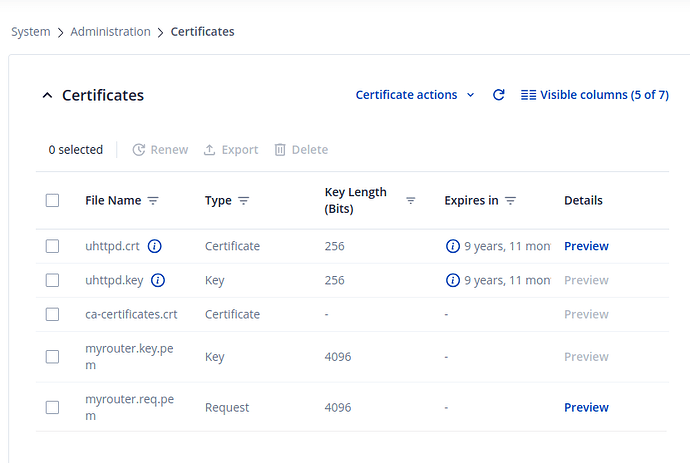
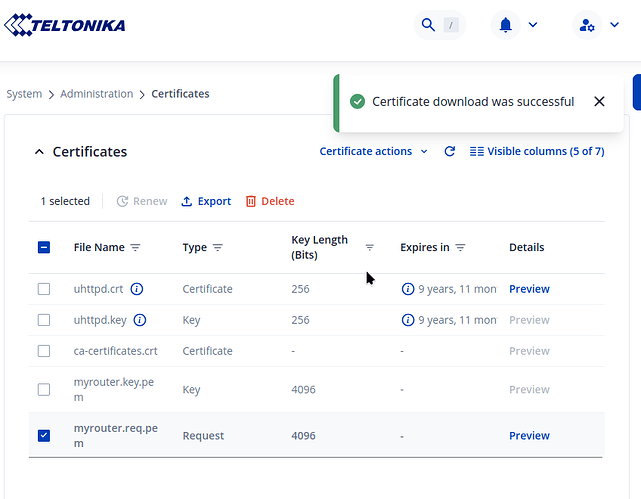
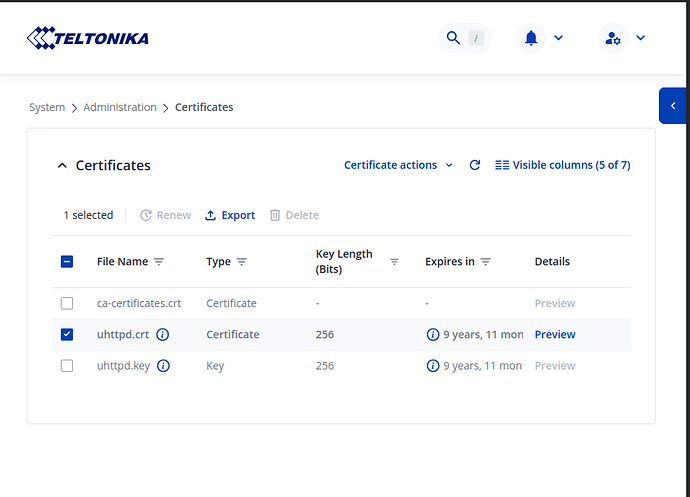
After clicking on “Create”, the device worked for a minute and then showed the key and the certificate request:
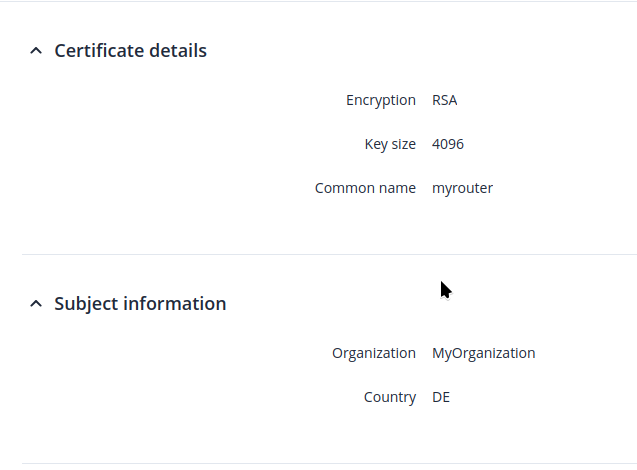
Clicking on Preview shows sensible data, but not the certificate request itself:
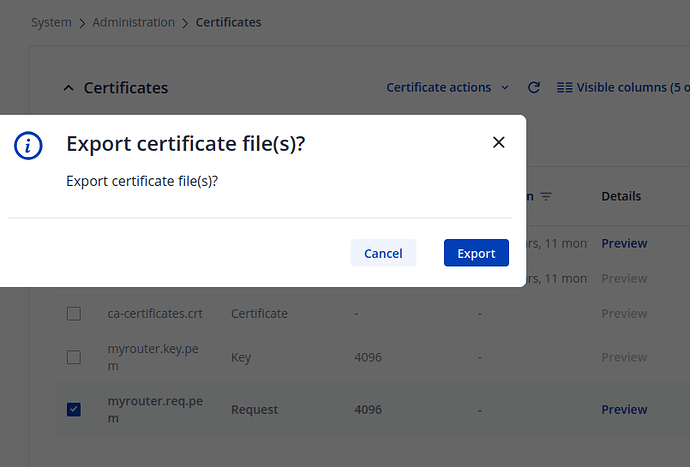
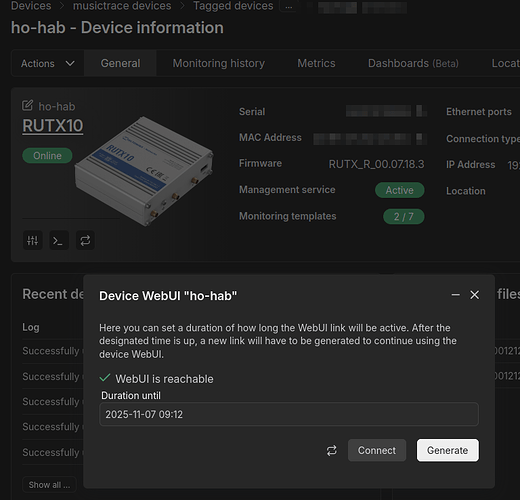
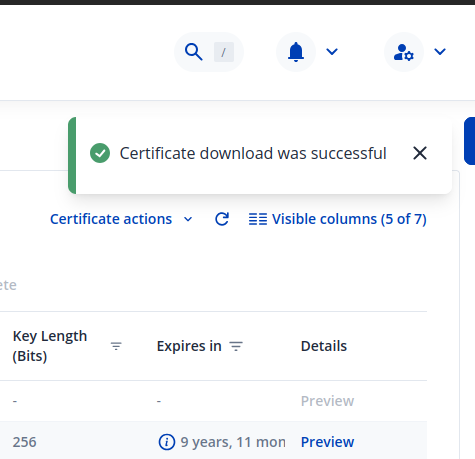
I then click the checkbox of the certificate Request and “Export” from the menu line:
Browser now happily says “Certificate download was successful”.
But, my Browser didn’t download anything. The downloads directory is empty. It looks to me like the RMS is somehow “eating” my download.
When I log on the device’s WebUI directly without going through the RMS, download of the certificate request is successful immediately. But that’s a luxury that I don’t always have; most of my devices are behind a NAT devices that I cannot control, and therefore cannot connect directly to my devices. That’s why I am using the RMS in the first place!
Where is my download going to?
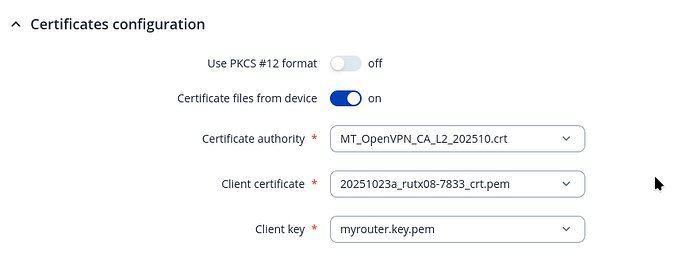
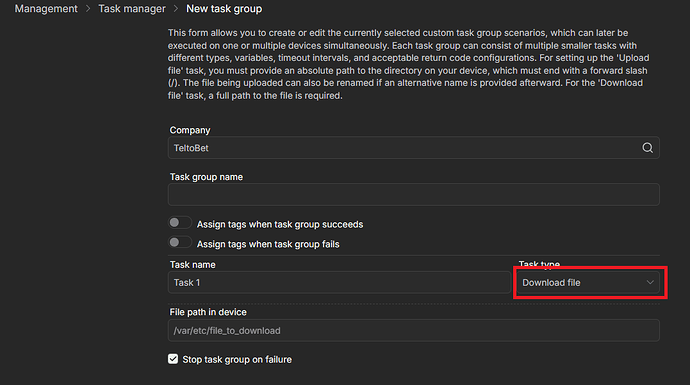
Now lets assume that everything was successful and I was able to create my OpenVPN configuration:
When I now enable the configuration, this appears in my log:
776 Thu Oct 23 15:13:16 2025 daemon.notice openvpn(inst1)[18045]: Note: cipher ‘AES-256-CBC’ in --data-ciphers is not supported by ovpn-dco, disabling data channel offload.
777 Thu Oct 23 15:13:16 2025 daemon.notice openvpn(inst1)[18045]: OpenVPN 2.6.9 arm-openwrt-linux-gnu [SSL (OpenSSL)] [LZO] [EPOLL] [MH/PKTINFO] [AEAD] [DCO]
778 Thu Oct 23 15:13:16 2025 daemon.notice openvpn(inst1)[18045]: library versions: OpenSSL 3.0.14 4 Jun 2024, LZO 2.10
779 Thu Oct 23 15:13:16 2025 daemon.notice openvpn(inst1)[18045]: DCO version: N/A
780 Thu Oct 23 15:13:16 2025 daemon.warn openvpn(inst1)[18045]: WARNING: No server certificate verification method has been enabled. See 2x HOW TO for more info. 781 Thu Oct 23 15:13:16 2025 daemon.warn openvpn(inst1)[18045]: NOTE: the current --script-security setting may allow this configuration to call user-defined scripts 782 Thu Oct 23 15:13:16 2025 daemon.warn openvpn(inst1)[18045]: OpenSSL: error:05800074:x509 certificate routines::key values mismatch: 783 Thu Oct 23 15:13:16 2025 daemon.warn openvpn(inst1)[18045]: Cannot load private key file /etc/certificates/myrouter.key.pem 784 Thu Oct 23 15:13:16 2025 daemon.err openvpn(inst1)[18045]: Error: private key password verification failed 785 Thu Oct 23 15:13:16 2025 daemon.notice openvpn(inst1)[18045]: Exiting due to fatal error`
I didn’t set a password on the private key!
What is going wrong here?
Sorry for being a nuisance, I am trying really hard to not be.
Greetings, Marc Haber